WordPress users beware of the newest vulnerability that hackers are quickly exploiting.
If you’re not running WordPress 4.7.2 or above then stop reading this article and update your WordPress version now.
Which WordPress Version Do I Have?
To find out which version of WordPress you have installed on your website, login to the admin area Dashboard.
There should be a dashboard widget called “At A Glance”. Your WordPress version number is displayed at the bottom of this widget.
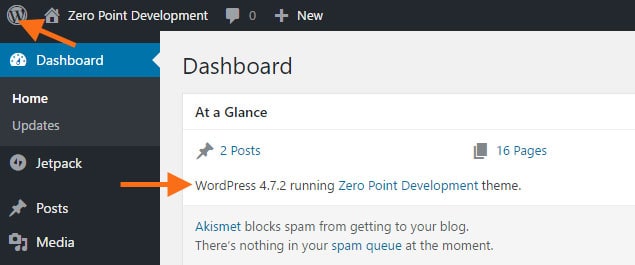
Alternatively you can click on the WordPress icon in the very top left corner of the site and this will open the About WordPress page.
The WordPress REST API Vulnerability
Hackers are using a vulnerability in a new feature that was added to the WordPress core in version 4.7 – the REST API.
This new feature allows external sites and apps the ability to get data from the WordPress site and (if logged in) update site data as well.
A bug was found that allowed anyone to remotely update data on any post or page without being logged in to the site. Yikes!
If you’d like to know the techincal issue of the bug please read the Sucuri blog post Content Injection Vulnerability in WordPress.
Sucuri have also posted an article about how hackers are trying to further exploit the bug by trying to run scripts on vulnerable sites – this is called Remote Command Execution.
Auttomatic, the organisation behind WordPress quick released a patch version 4.7.2 which fixed the bug, however, it may not automatically update on all sites.
It is important to keep WordPress Core, themes and plyugins up to date regularly to ensure security bugs are patched. We update at least once a week if not every other day. It only takes 5 minutes of your day to check run updates for a single site so there’s no excuse not to do it.
As of writing it is estimated that 1.5 million web pages have been defaced using the exploit so it is uber important that you check and update your WordPress version now!
